According to the latest stats, mobile ad fraud is costing marketers an average of $50 million per day. According to Intercetpd, from 2018 – 2019, mobile ad fraud has seen a 13.2% YOY for Android and has experienced a rapid 17.3% YOY increase for iOS. Mobile ad fraud is diversifying with SDK spoofing rising, and lesser sophisticated forms, such as device farms decreasing.
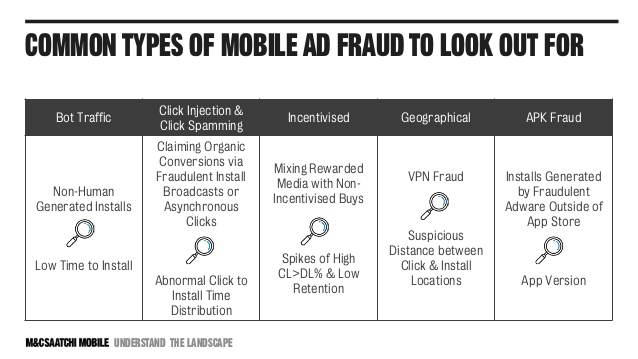
There are numerous types of ad fraud. However, we’re here to discuss what to do once you have detected the mobile ad fraud.
Dealing with mobile ad fraud after it has been detected requires a combination of technology, data, and the right people. There are numerous metrics and data-points and patterns to look at when attempting to detect mobile ad fraud. We will delve into some methods of protection after detection.
Mobile Ad Fraud prevention requires a combination of technology, data, and people. The funnel from impression to post-install gives you important clues. So, you should learn how to read this funnel.
Know Your Enemy
There are many types of mobile ad fraud. They can manipulate impressions by serving invisible banners at a time, or perhaps having multiple display ads stacked upon each other (aptly known as ad stacking), there are like farms, device farms, and phone farms that to carry out fraudulent actions like a click or install. Some of these farms are human-operated, some are device operated. All are fraudulent. Thus, the best form of defense is awareness. Understand what potential threats exist. How mobile ad fraud happens. What are the potential areas of weakness? Education and awareness if your best form of defense against mobile ad fraud.
Monitor Relevant Metrics

There are three important metrics to let you identify mobile ad fraud.
One of them is “time to install (TTI)”. Even though it depends on the internet speed and the app size, installing the app after the click takes more than 30 seconds generally. However, a common pattern of ad fraud is when numerous installs take place within 10 seconds. Thus, it is important to monitor the TTI times of your app.
Another metric is “clicks to install time (CTIT)”. This is the time from the first click, to when the app was opened. When CTIT times are too low, this can be an indication of click injection or SDK spoofing. When CTIT times are too high, this could be an indication of click spamming. However, one particular concerning install should not tarnish a whole ad network or publisher. It is important to look at their distribution. If this pattern of concerning CTIT times is repeated enough to form a pattern, then this might indicate that publisher or ad network is fraudulent.
The last point you can look is the combination of IP address and User-Agent. There could be a high number of app installs from the same IP on a given day. You can deduce it by analyzing IP addresses. However, IP addresses can be hidden. In such cases, the device’s User Agent gives you a more deductive path. If a fraudster is more advanced and uses a Proxy, you need to focus on database work. Thanks to this analysis, you can explore IP mismatch, IP quality, and duplicate IPs.
Create A Pattern
Patterns are going to be the single most important point of detection. Unfortunately, there is no one “ad fraud” metric. Ad fraudsters do not tag their installs with the “fraudster” tag. There are numerous types of fraud, perpetrated by numerous different fraudsters. Thus, it is only natural that detecting fraud requires an array of methods and points of detection. Here are some patterns to look out for:
-
- An abnormal pattern of CTIT (click to install times) distribution. CTIT times vary greatly per install. That is why it is more important to look at the overall CTIT distribution of each publisher, or ad network, affiliate, etc. If an abnormally high or low CTIT emerges, then this might be an indication of click spamming or click injection. You might want to blacklist this source.
- Too many outdated devices or operating systems? Too many downloads from users with an outdated operating system? Possibly a device farm.
- Too many clicks or downloads from another country? Too many clicks from outside where your campaigns are targeted? This could be a strong indication of fraud.
- Excellent KPIs but low activity. Are your campaigns absolutely excelling, yet revenue is down? Are ad-clicks and registrations up, however, session time is down? Engagement (although also easily fooled) is one indication of genuine activity. If this is not going up along with your increased advertising acquisition, either your campaigns are not targeting the right audience, there is a product or service issue, or you’re experiencing ad fraud.
These are just some of the myriad of metrics, patterns, and data-points to look out for when attempting to detect and prevent mobile ad fraud. Additionally, many of the above examples do not certainly indicate fraud is small doses, however, if enough of these concerning data or incidents emerge and begin to form a pattern, then it may point to mobile ad fraud.
Blacklist
Once you determine a pattern, ad fraud becomes a lot easier to deal with. You can add specific IPs and publishers to your blacklist for future reference. So, you can curate your own database comprising of blacklisted IPs and publishers. This is an important step, as often genuine ad networks or affiliates can unknowingly be corrupted by fraudulent sub-publishers. Providing this information back to the ad network, or affiliate or source, given the source a chance to clean up their traffic.
However, this is not always the case. Sometimes, specific ad networks or other sources are aware of the fraudulent activity that exists. They merely balance this out with genuine traffic in order to evade detection.
Demand Transparency
Demand transparency from all of your sources. Transparency means being able to access raw data. If you decide to work with a mobile ad fraud prevention tool, keep in mind that it is important to see clearly how well your mobile ad budget is being spent. So, ask for the complete transparency of your data in reporting, pricing, and ways of working.
Compare the data from your MMP (mobile measurement partner) and your own app data, or business intelligence tools. Compare the data between your ad network and your own data. Compare every data source. How do you do this and where do you start? A good place to start with is revenue. Is the revenue reported by your MMPs or attribution providers matching what revenue you have actually generated? If something does not add up, then ask the question.
Note: this data will be extensive. However, it is only through the raw data that you can compare clicks to clicks, installs to installs.
Work With Trusted Partners
You can work with a trusted partner in the industry. As App Samurai, we use sophisticated machine-learning algorithms to help you detect, prevent, and fight against mobile ad fraud systematically. All channels, platforms, partners, ad networks, affiliates, and so forth are affected by mobile ad fraud. Thus, it is wise to partner with the right source that acknowledges that fraud exists, and has communicated their plan in dealing with it.
Perhaps compare multiple sources, to check their anti-ad fraud capabilities.
And last, but certainly not least, work with a source that actively blocks fraudulent clicks and installs, before the fraudulent activity has been paid for.
If you’re currently with a particular ad network, affiliate or digital agency, ask them: what is your strategy for dealing with ad fraud?
Conclusion: What to do After Mobile Ad Fraud is Detected
Mobile ad fraud is a tricky playground, filled with bad-actors, corrupt data and unknowing participants, innocently sliding down the fake slippery dip. However, simply being aware and understanding of this complex and evolving world will put you ahead of your competitors. Get comfortable with examining your data (app data, MMP data, business intelligence data). Get to know unfamiliar metrics, such as Google Store Referrer Times, CTIT and App Version. Ask your sources: what is your mobile ad fraud prevention plan? Develop a black and white list of sources and publishes you trust, and you know are fraudulent. Most importantly, work with trusted sources and partners.
If you’d like to discuss how App Samurai simultaneously promotes your app, whilst securing our data and blocking fraudulent clicks and installs, get started here.
Could not generate text at this time.
In the battle against mobile ad fraud, knowledge truly is power. To effectively combat fraudsters, you first need to understand the subtle (and sometimes not-so-subtle) ways they operate. For instance, ever heard of click injection? It’s a sneaky tactic where fraudsters trigger fake clicks just before an app is installed, claiming credit for organic conversions. Then there’s SDK spoofing, where cybercriminals manipulate app data to fake installs and in-app events. These tactics may sound intimidating, but the good news is that they leave a trail of breadcrumbs in your data. By closely examining metrics like click-to-install time, abnormal patterns in user behavior, or unusually high conversion rates from specific sources, you can start to uncover fraudulent activity. Think
Detecting mobile ad fraud is a bit like being a detective in the fast-paced world of digital marketing—it requires sharp instincts, the right tools, and a solid understanding of the culprits you’re up against. One of the first steps is to examine the entire funnel, from impressions to post-install events, as this is where fraudulent activity often leaves its trail. Look for suspicious patterns, like unusually high click-through rates with no conversions or sudden spikes in installs from unlikely regions. These anomalies could point to fraud tactics like click spamming or bot-driven installs. It’s also essential to leverage fraud detection tools that can flag SDK spoofing, click injection, and other advanced schemes hiding in plain sight. Remember, fraudsters are constantly evolving their methods, so staying